Explore and Launch: New Example Pipelines Now Live 🚀
You can now explore Buildkite with a library of live, working example pipelines! No setup or sign-up required. It’s the fastest way to see what Buildkite can do, and start building with confidence.
🆕 Public example pipelines are:
- Fully interactive and backed by real GitHub repos
- Searchable on the Examples Gallery
- Integrated directly into the pipeline creation form
- Embedded in the YAML steps editor as inline inspiration
- Always fresh, thanks to scheduled builds and Algolia-powered syncing
🔥 Why it matters
Starting from scratch in Buildkite used to be like opening a blank cookbook - you had the ingredients, but no idea how to bring them together. Now with real-world examples, you get the full recipe in action! You can explore pipelines that run in real time, show actual build logs, and are easy to fork and modify.
These examples span a wide range of use cases, including:
- 💻 Multiple languages and frameworks
- 🔄 Dynamic Pipelines
- 🐳 Docker builds
- 🏛️ Monorepo patterns
- 🚦 Concurrency groups
- 🛑 Block steps
- 🪝 Custom hooks
...and many more!
Whether you’re evaluating Buildkite, onboarding a team, or looking for inspiration, examples give you a fast, safe way to explore what’s possible.
- ✅ It’s onboarding without the guesswork
- ✅ It’s demos without the setup
- ✅ It’s Buildkite unboxed
🪄 See Example Pipelines in Action
Examples Gallery
Explore the new Examples Gallery, browse the public GitHub repos, and see real pipelines running live on Buildkite.
Examples in Product
This walkthrough shows how easy it is to go from creating a new org to running your first build using examples directly in onboarding, pipeline creation, and the YAML steps editor.
🆕 Available to try out!
- Browse the Examples Gallery
- See our live Public Pipelines on Buildkite
- See our Example Repositories
This feature is now live for all users 🚀
Got an idea for a new example? Let us know or contribute on GitHub.
Sarah
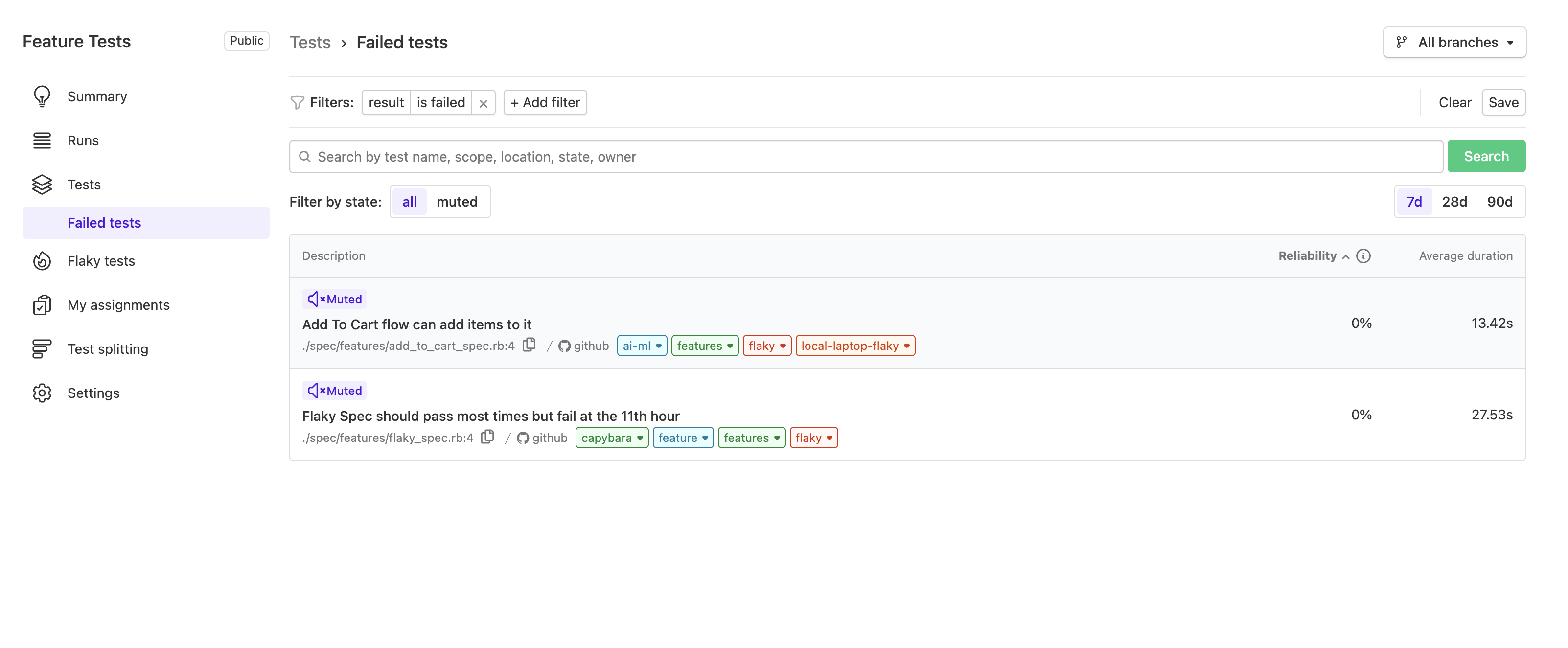
Improved Flaky Test Management in Test Engine
We're excited to share that Test Engine has rolled out a new and improved way to manage flaky tests! Utilizing customizable columns we have moved flaky tests into a new saved view.
This change gives you power to customize the views that matter most to you. 🚀
What's New
"Flaky" Saved View:
View all actively flaky tests in one place. Flaky tests are now clearly labeled, making it easier to filter and manage them at a glance.
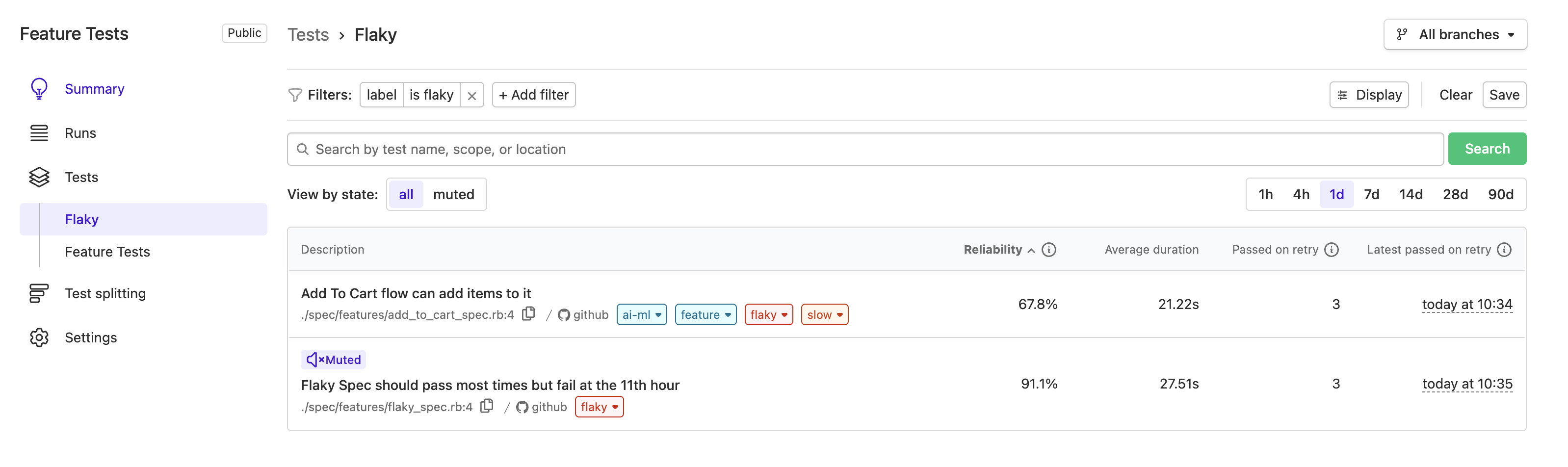
Remove the Flaky Label:
If you've fixed a flaky test, simply remove the flaky label from its test page. This automatically updates your Flaky saved view.
Team-Based Filtering:
Use the new Ownership filter to view all tests owned by your team(s). You can save this view for quick access anytime.
Katie
Customize Test Engine Tests View
You can now customize which metrics are displayed in the Tests View to better suit your needs. We've added new metrics to provide deeper insights into your test performance to help you make more informed decisions about your tests.
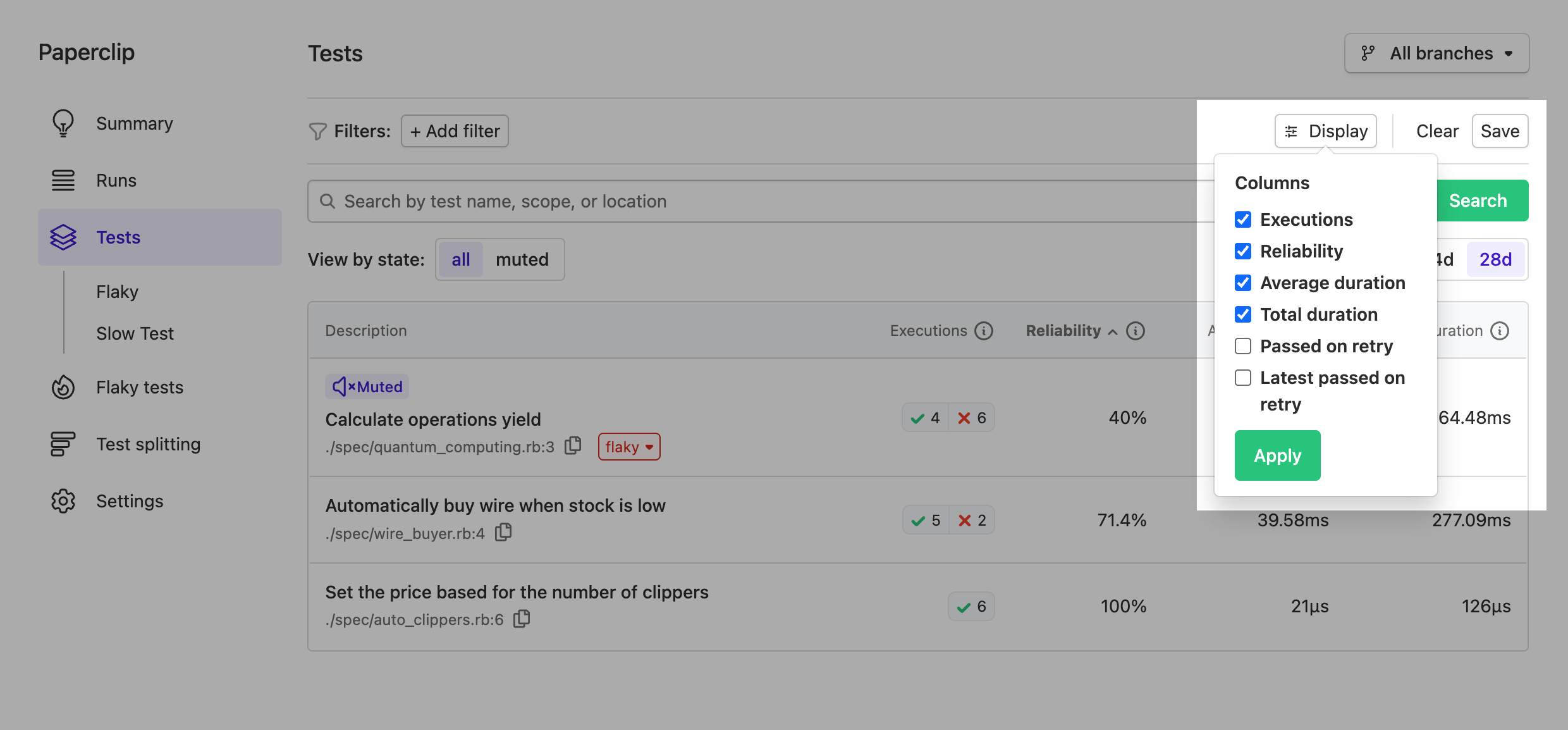
Available metrics
-
Reliability
The reliability of the test within the selected date range and filters. Calculated as the percentage of 'passed' executions out of all 'passed' and 'failed' executions. -
Average duration
The average time taken to execute the test within the selected date range and filters. -
Executions 🆕
The number of times the test was executed within the selected date range and filters, grouped by result. -
Total duration 🆕
The cumulative time spent on all test executions within the selected date range and filters. -
Passed on retry 🆕
The number of times the test reported both 'failed' and 'passed' results on the same commit SHA within the selected date range and filters. -
Latest passed on retry 🆕
The most recent occurrence where the test reported both 'failed' and 'passed' results on the same commit SHA within the selected date range and filters.
Saving the customizations
Building on top of our Saved views, you can also save your customizations to tailor the view to your specific workflow.
Naufan
Mac Hosted Agents Now Running on M4 Pro Hardware
All macOS workloads on Buildkite hosted agents have recently been upgraded to run on Apple’s latest M4 Pro generation hardware - delivering better price-performance for your CI builds.
The M4 Pro chip delivers meaningful improvements over the previous generation (M2 Pro), including:
- Up to 30-45 % faster CPU performance in real-world Xcode builds and test runs
- Next-generation GPU architecture for smoother UI testing and graphics-heavy tasks
- Higher memory bandwidth for faster access to large codebases and build artifacts
Starting today, we’ve updated our Mac shapes with two new M4-optimized options:
- Medium (6x28)
- Large (12x56)
These new shapes supersede the legacy M2-based shapes, which will be deprecated on July 31. Customers are advised to update any existing queues to use the new M4 shapes ahead of time to avoid disruption.
- Enterprise customers: Your account team will reach out to support this transition.
- Pro customers: You’ll receive an email shortly with more details and instructions for updating existing queues.
Have questions or need help? Reach out to us at support@buildkite.com
With super fast startup times, clean ephemeral environments for each job, the latest Xcode updates and developer tools ready to go - and now powered by M4 Pro - Buildkite Hosted Agents for macOS are built for fast, reliable CI at scale.
Daniel
Buildkite Agent Stack for Kubernetes Improvements: Easier to Adopt, Scale, and Maintain
Over the past few months, we’ve made a series of improvements to the Buildkite Agent Stack for Kubernetes, focused on simpler setup, improved efficiency, and reliable scaling. Bringing us to version 0.29.2, these updates are the result of our sustained engineering investment in our Kubernetes integration, designed to help platform teams reduce overheads and ship faster with greater confidence.
What’s improved
- Simpler setup: You can now deploy a stack with just a single cluster-scoped agent token. Previously-required configuration is no longer required: the GraphQL token, organization slug, and cluster UUID are no longer required or used. Default queue behavior is also streamlined: the stack now defaults to the cluster's default queue, rather than a queue called
kubernetes. - Better scaling under load: The internals of the controller have been reworked to more efficiently discover and handle large volumes of jobs, even in high-concurrency environments. Job environment variables are now passed between job containers directly, reducing per-job Kubernetes object sizes. Fixes to tag matching and queue routing ensure that job lifecycles are handled correctly by the controller.
- More secure by default: GraphQL tokens, which have many capabilities that are unnecessary for running a stack, are no longer used. Everything now runs on the REST API using scoped agent tokens, and we’ve started internal testing of scoped secret support for more secure isolation across pipelines and environments.
- Greater configurability: Helm chart values now expose settings for things like job name prefixes, controller env vars, resource limits, and pod annotations, giving teams more flexibility to tune the stack for their environment with out-of-the-box controls.
- Better errors and observability: Error messages for Kubernetes job creation failures now include the job spec in YAML form, making it easier to diagnose misconfigurations. Prometheus metrics have been updated to support monitoring stack performance. Stack-level job failures are now reported to Buildkite using a new
stack_errorsignal reason.
Recent releases
These improvements have been rolling out since March, with highlights in the following versions:
- v0.29.2: Fixes a permissions issue within job pods, upgrades Buildkite Agent to v3.100.1.
- v0.29.0: Introduces cluster-only agent support, removes the
queue=kubernetesdefault tag, adds better error output and tag matching logic. - v0.26.0 through v0.28.2: Improvements to cleanup, resource management, default queue handling, plugin mounts, GraphQL removal, and REST-only job fetch.
If you're running the Buildkite Agent Stack for Kubernetes, now’s a great time to upgrade. These changes simplify how you manage agents, reduce the number of moving parts, and make builds more predictable at scale. To get started, check out the official documentation.
Josh
Vitest Support for JavaScript Test Collector
We're excited to announce Vitest support for our Buildkite JavaScript Test Collector, expanding our test framework coverage for Test Engine.
With Vitest support in the JavaScript Test Collector, you can now:
- Collect test results from your Vitest test suites
- Track test performance and flakiness over time
- Benefit from Test Engine's powerful analytics and insights
- Automatically quarantine flaky tests
To begin using the Test Engine with Vitest, follow the instructions in our JavaScript Test Collector documentation.
Naufan
The next phase of the build page experience
The new build page has been updated with a bunch of improvements that now make it easier to focus on what matters, move faster through your builds, and tailor the interface to suit how you work. Whether you're reviewing a failed test, scanning logs, or debugging pipeline performance, these updates help streamline the experience across pipelines of all shapes and sizes.
With so many changes landing, we thought why not record a video to walk you through them all.
Key changes
New build header
We've redesigned the build header into a more condensed version—reducing noise on the page, and helping to draw more attention to the things that need actioning: failed steps and annotations. With this revision, the build status is also now always visible regardless of how you've configured the build interface.
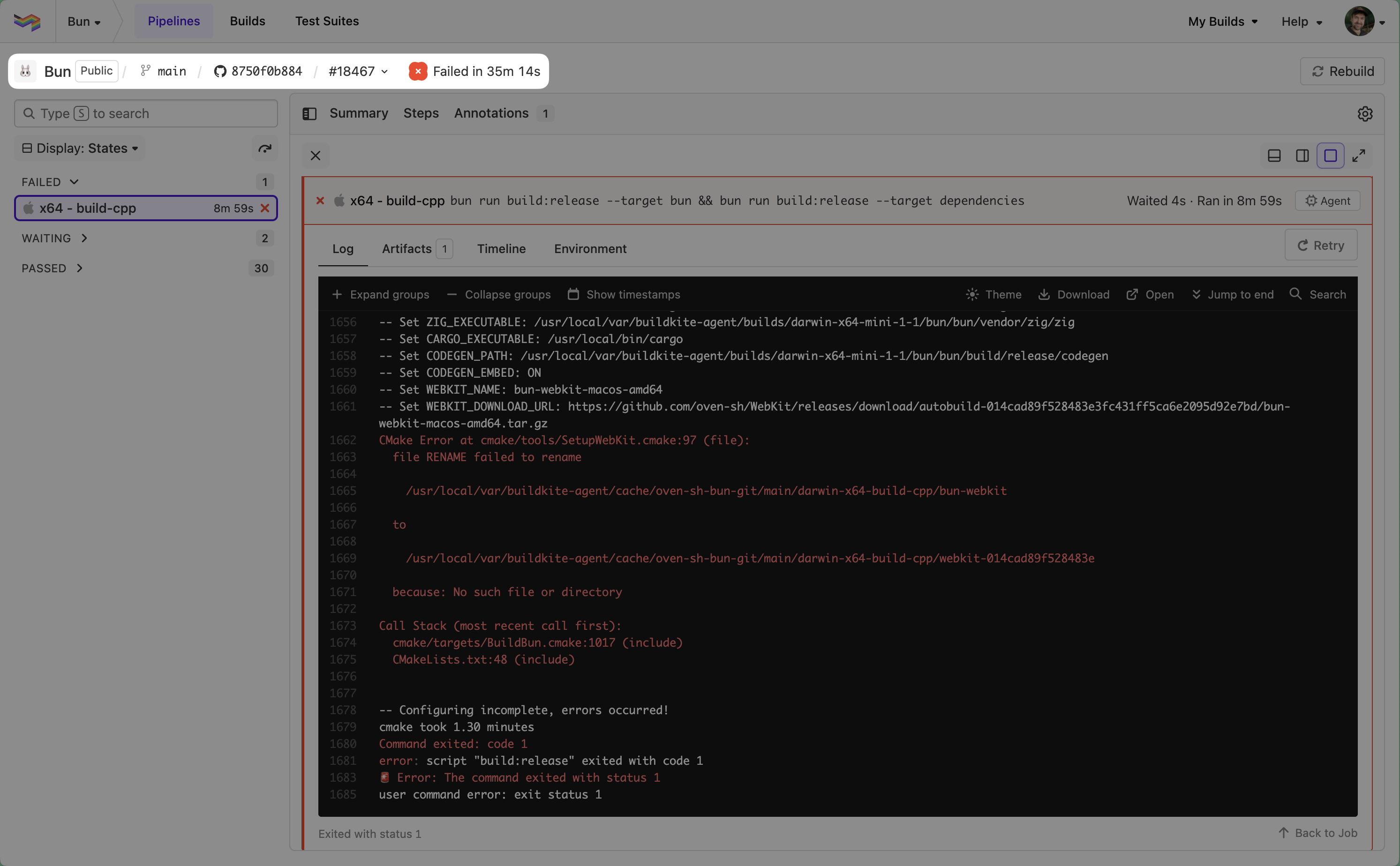
Overview tab
There's a new overview tab that contains high-level build information—such as the commit message, build creator, build trigger and much more.
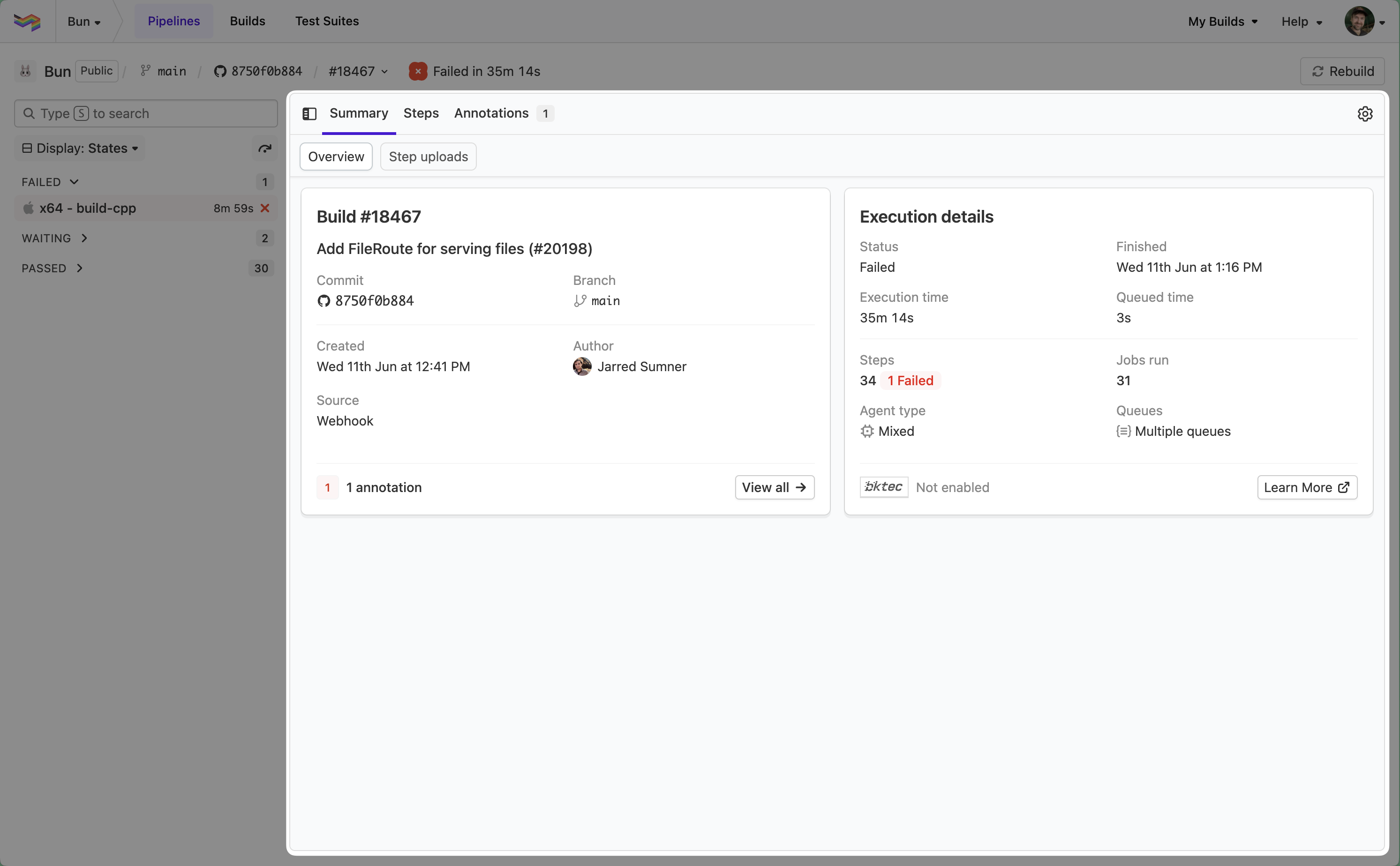
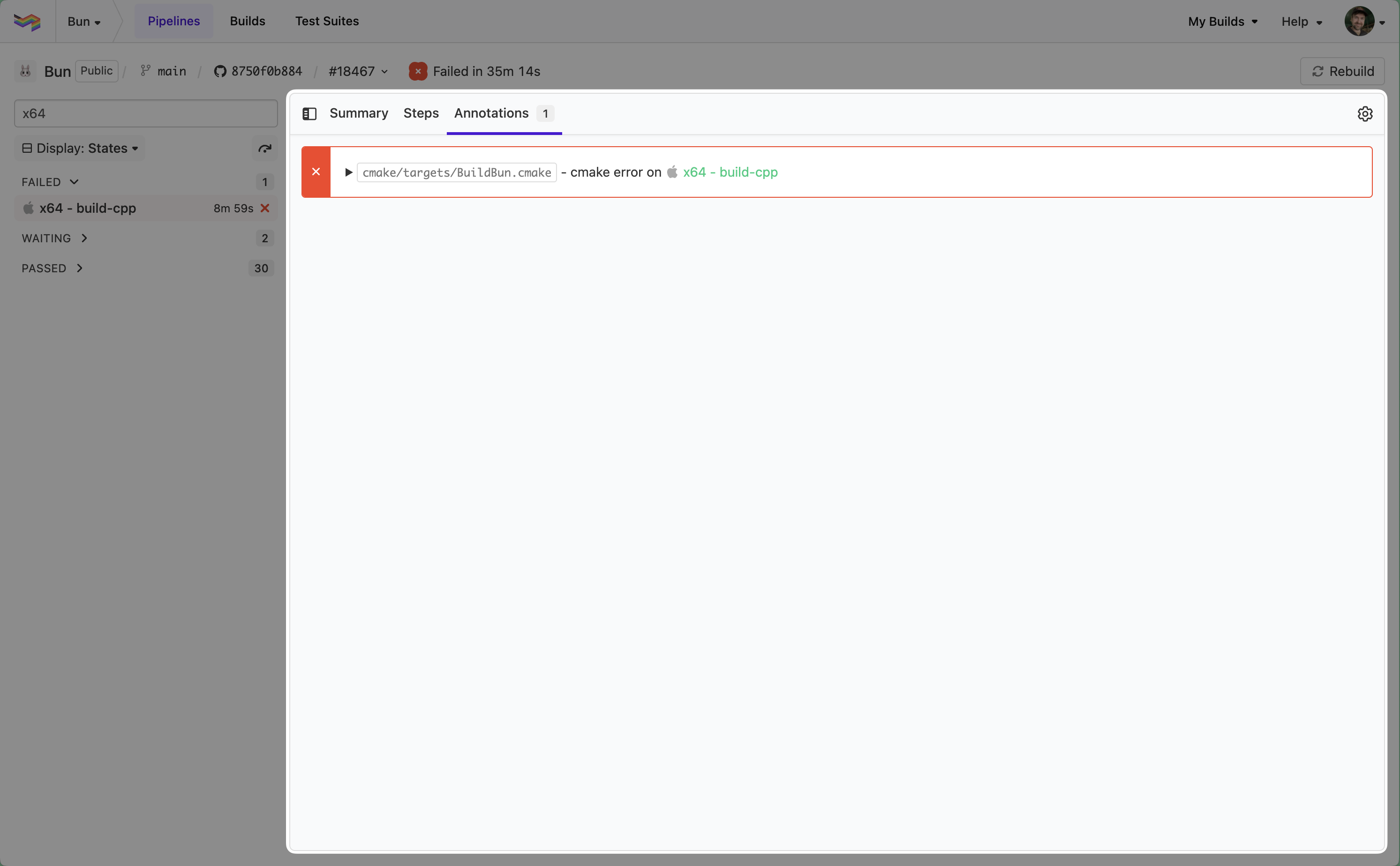
Annotations tab
The annotations have been moved into a top-level tab, making them easier to find and use.
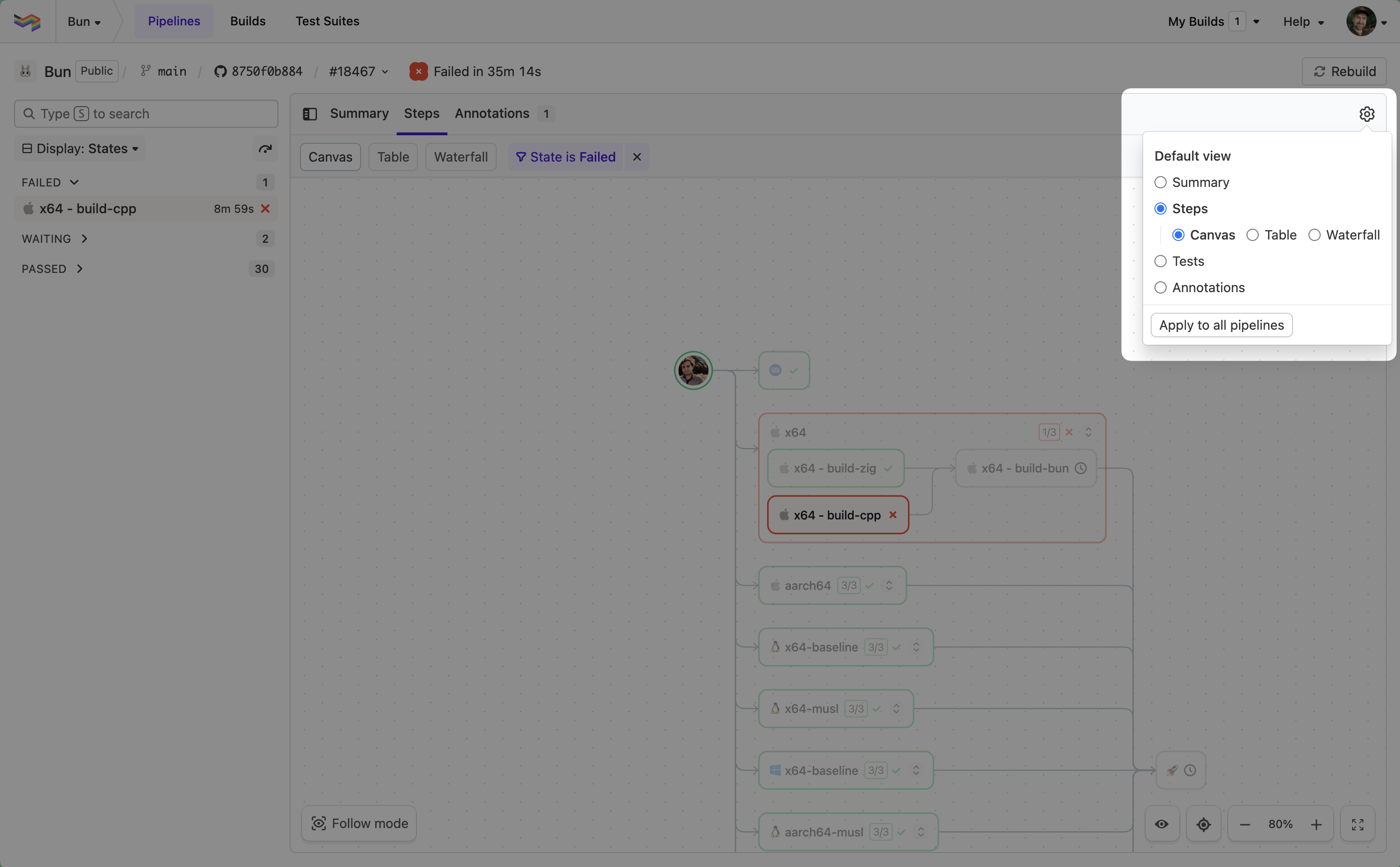
Configurable default view preferences
You can now set a personal default view preference—allowing you to control where you start when opening a build. This can be applied globally or customized per pipeline.
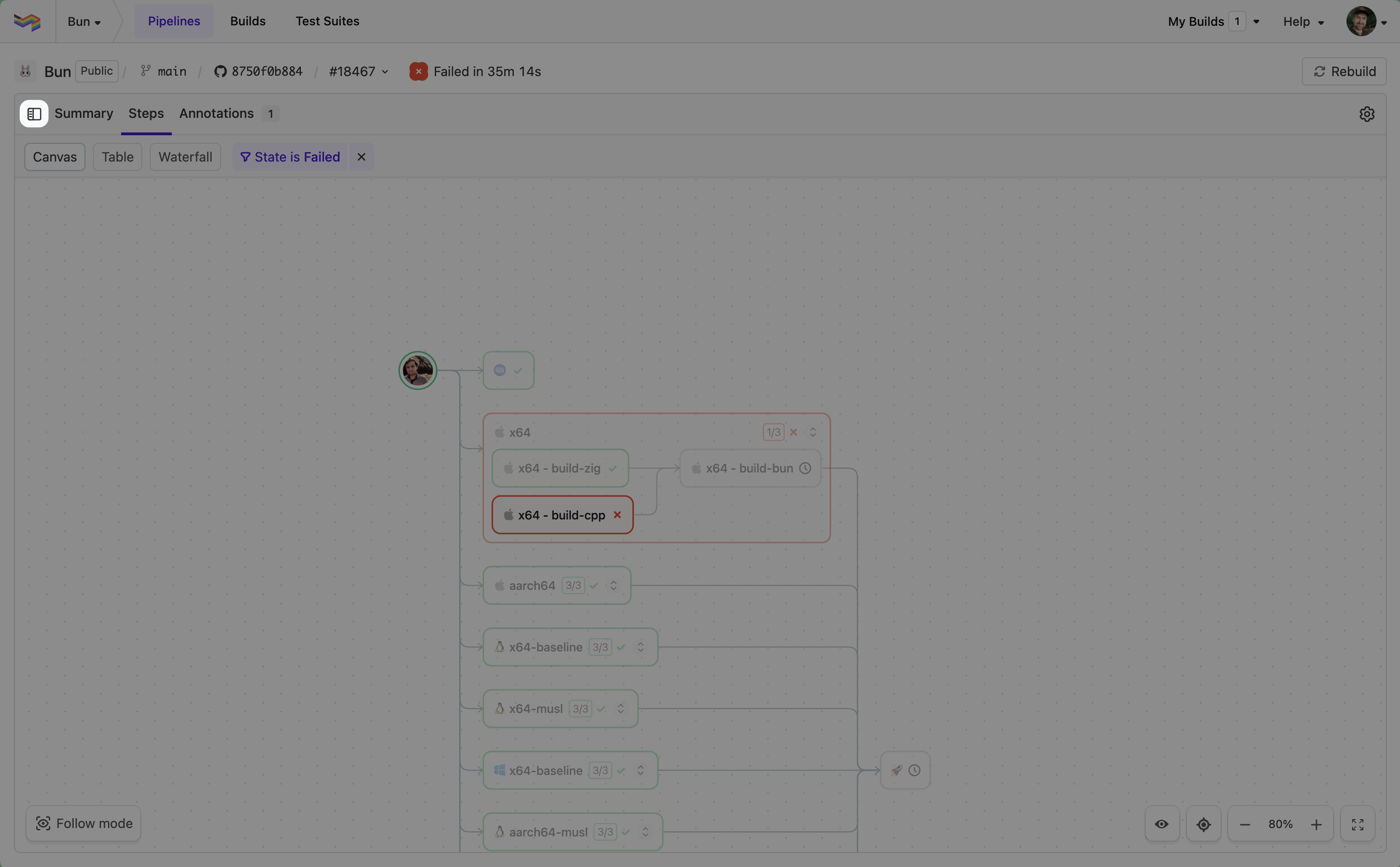
Collapsible sidebar
The sidebar can now be toggled open or closed, giving you more control over the layout when diving into a job or viewing other parts of the build.
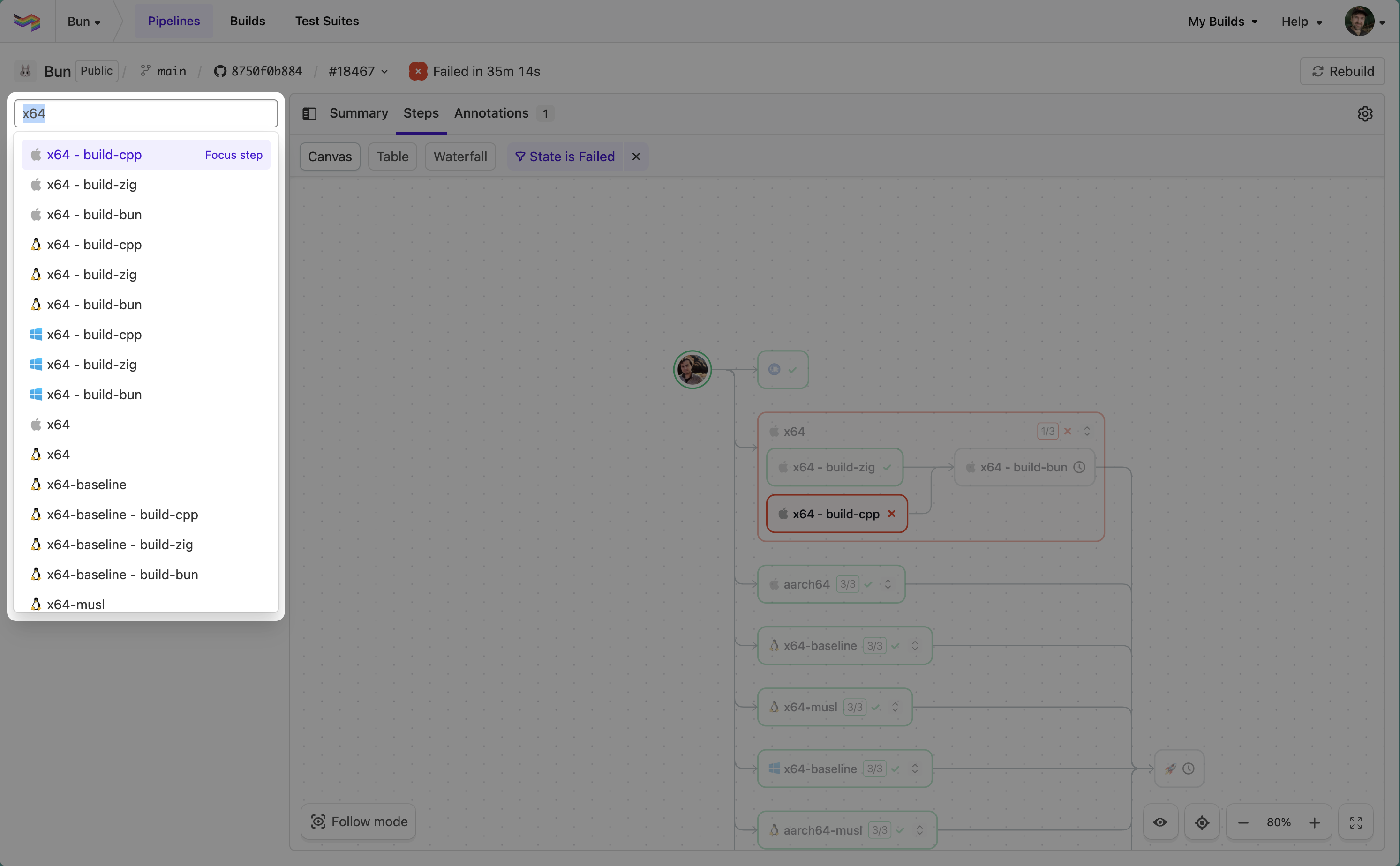
Step search in the sidebar
We've added a new search, allowing you to find and jump to steps quickly across your build.
Keyboard shortcuts:
S: Open search boxEnter: Open the stepShift+Enter: Focus on step in current step view
Jump to failure
The jump to failure action has moved into the sidebar, making it possible to cycle through failures wherever you are in the build.
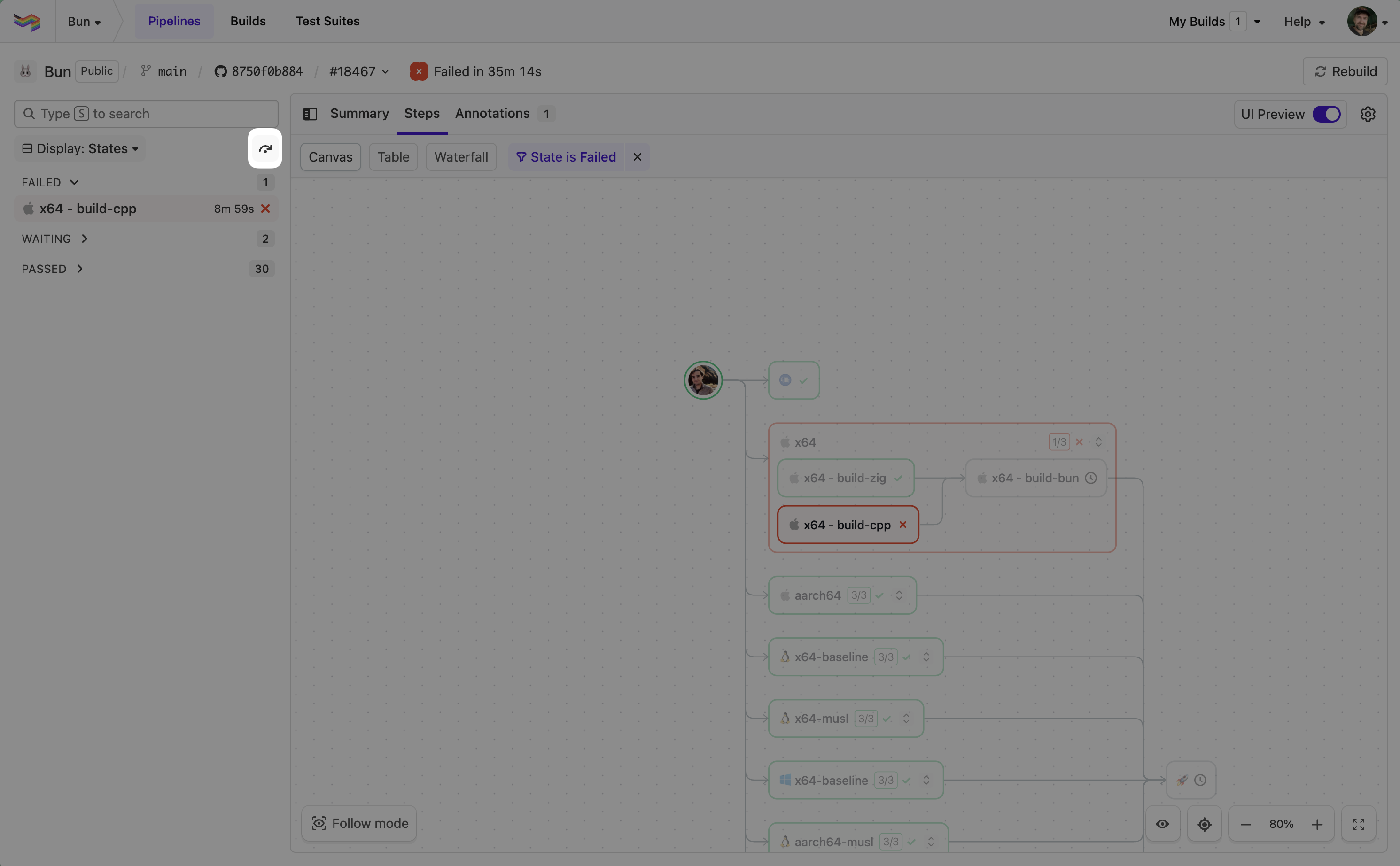
Other notable improvements
- Log performance: Improved rendering performance and added support for searching within collapsed sections.
- Canvas unblock UX: Clicking an unblock step now opens the unblock dialog directly.
- Smarter canvas focus: For large pipelines that don't fit neatly on the canvas, we now focus on the first failure—or the first step if all steps pass.
- Canvas zoom constraints: Zoom levels are now constrained to prevent unreadable dependency graphs.
- Resizable table columns: Table view now supports column resizing for improved readability of long job labels.
- Responsive improvements: Improved layout behavior on smaller screens to avoid overlaps and horizontal scrolling.
Thanks again for all the feedback which continues to help us shape each release.
Chris
GitLab.com Commit Status Support
We've added support for GitLab.com commit statuses to Buildkite Pipelines ✅
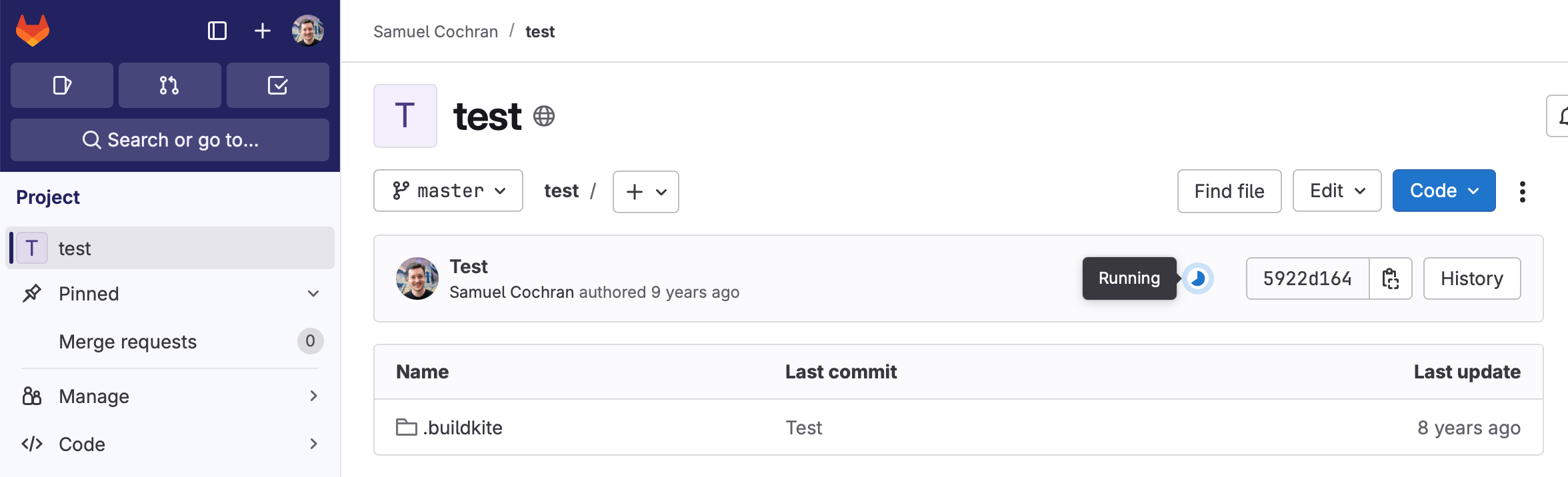
Buildkite can now send status updates to GitLab for each build state (scheduled, started, running, passed, failed, blocked, canceled, skipped). Status updates appear on commits and merge requests in GitLab. These link back to the corresponding Buildkite builds.
Turn this on today by connecting to GitLab.com:
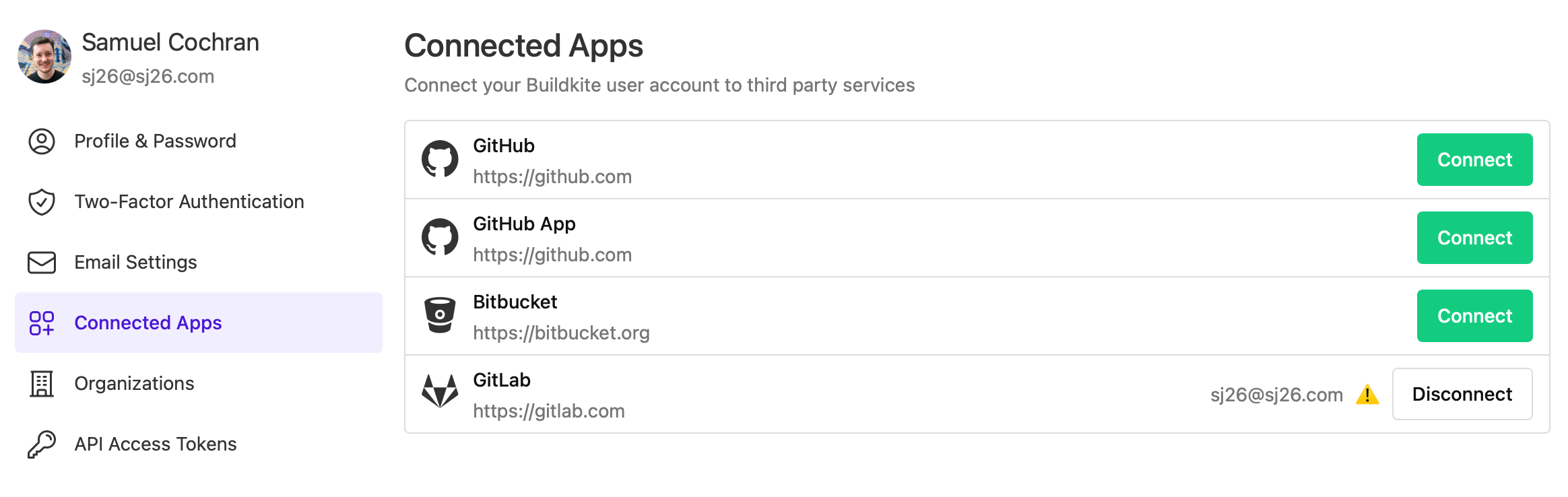
Then update your favorite pipeline's repository settings page to turn on commit status reporting ✨
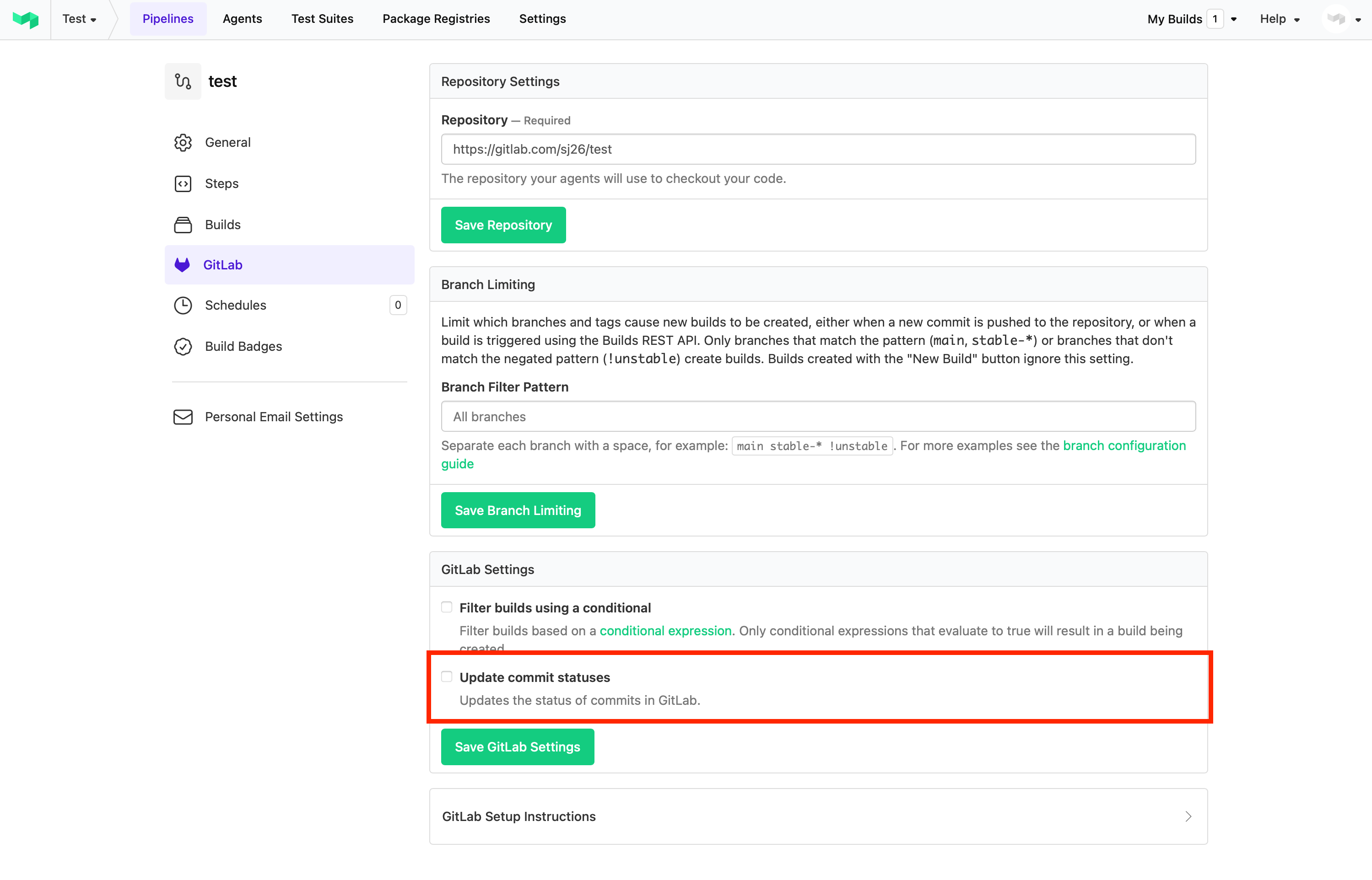
For more details, see our GitLab documentation.
Samuel
Send Slack notifications from Test Engine
You can now send Slack notifications from Buildkite Test Engine!
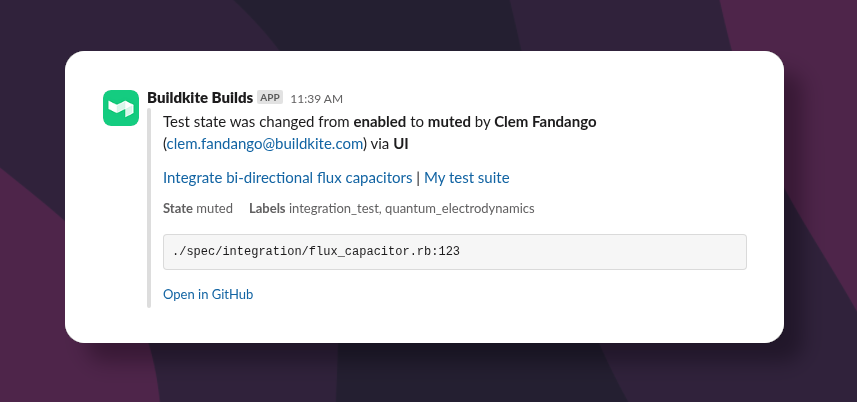
Slack notifications can be triggered when a test state changes, or when a test label is added or removed.
Additionally Slack notifications can be filtered to only tests owned by particular teams.
Read more about Test Engine Slack notifications.
Malcolm
Flaky Resolution deprecation
The Flaky Resolution feature is being deprecated and will be removed for all users in the coming week.
You can continue managing flaky tests by removing the flaky label. You can review all currently flaky tests via the Tests page, by filtering for tests with the flaky label.
Meghan
My Assignments deprecation
The My Assignments feature is being deprecated and will be removed for all users in the coming week.
Users can continue to review tests owned by their teams using the filtering functionality on the Tests and Flaky tests pages.
As part of this change, the Flaky Summary Mailer will also be updated to show the flakiest tests owned by your team, rather than those that were previously assigned.
Katie
Send webhooks from Test Engine
You can now send webhooks from Buildkite Test Engine!
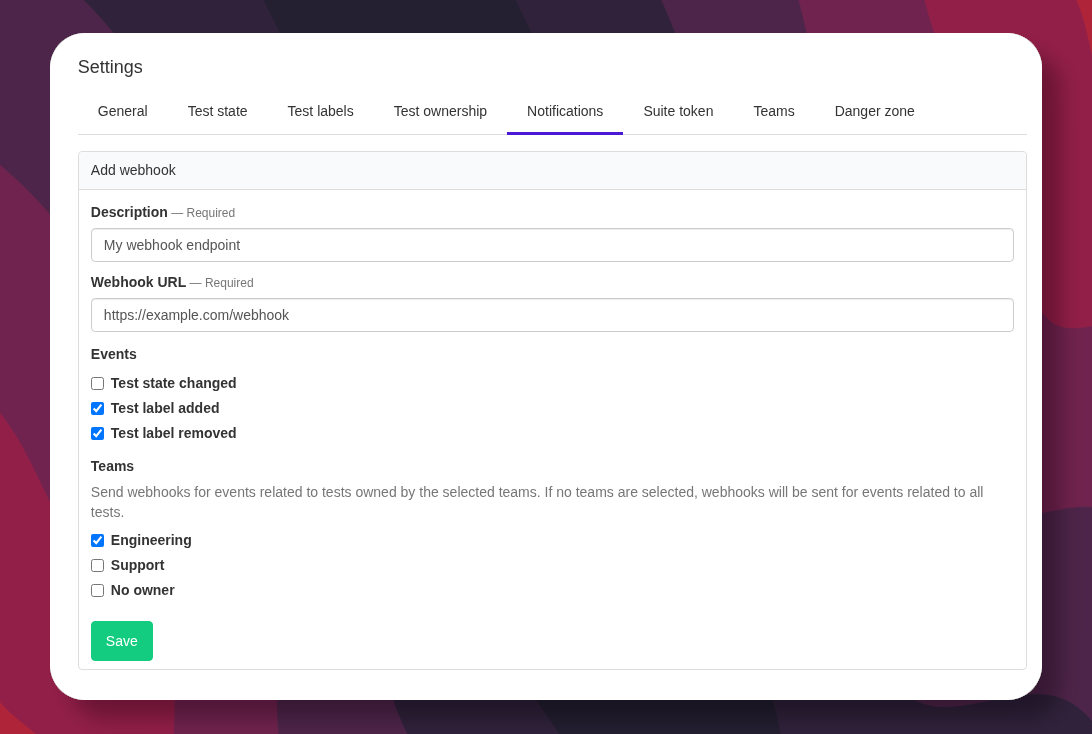
Webhooks can be triggered by the following events:
- Test state changed
- Test label added or removed
Additionally webhook events can be filtered to only tests owned by particular teams.
Read more about Test Engine webhooks.
Malcolm
Saved filters in Test Engine
You can now save your favorite test filters in Test Engine for quick access.
The new filter bar in the test list lets you add filters using execution tags and test labels. Once you've set up a view you like, click Save to name it. Your saved filters will then appear as a view in your suite navigation for easy access.
Meghan
Introducing Portals: Authenticated endpoints for GraphQL operations
Buildkite Portals are user-defined GraphQL operations exposed via authenticated URL endpoints — offering a new, secure way to access the Buildkite API.
Designed with machine-to-machine operations in mind, Portals are not tied to user-owned access tokens. Instead, they use ephemeral, scoped tokens that can only perform the operations defined in an approved GraphQL document.
Key benefits of Portals include:
- Scoped access — Tokens are restricted to the exact operations defined by organization admins. This enables fine-grained, least-privilege access to your Buildkite data.
- Ephemeral tokens — Tokens are short-lived and single-purpose, ideal for secure machine-to-machine communication.
- User-invoked flow — Optional interactive flows allow users to generate tokens on-demand, similar to OAuth.
- Userless authentication — Tokens are not tied to any individual user, avoiding disruptions if team members are removed.
Getting started with Portals
Portals can be created by administrators from organization settings page. Each portal is assigned a unique endpoint with the following URL structure: https://portal.buildkite.com/organizations/{organization.slug}/portals/{portal.slug}
Portals support passing variables to enable dynamic operations and offer multiple authentication mechanisms for flexibility and security.
For more information, see the Portals documentation.
Himal
Python support for test splitting and auto-quarantining 🚀
Buildkite Test Engine now supports test splitting (smart bin packing for faster CI) and auto-quarantining (automatic detection and isolation of failing tests) for Python PyTest suites.
- ✅ Cut down your critical path time.
- ✅ Keep flaky tests from blocking your pipeline.
- ✅ Spend less time on manual triage.
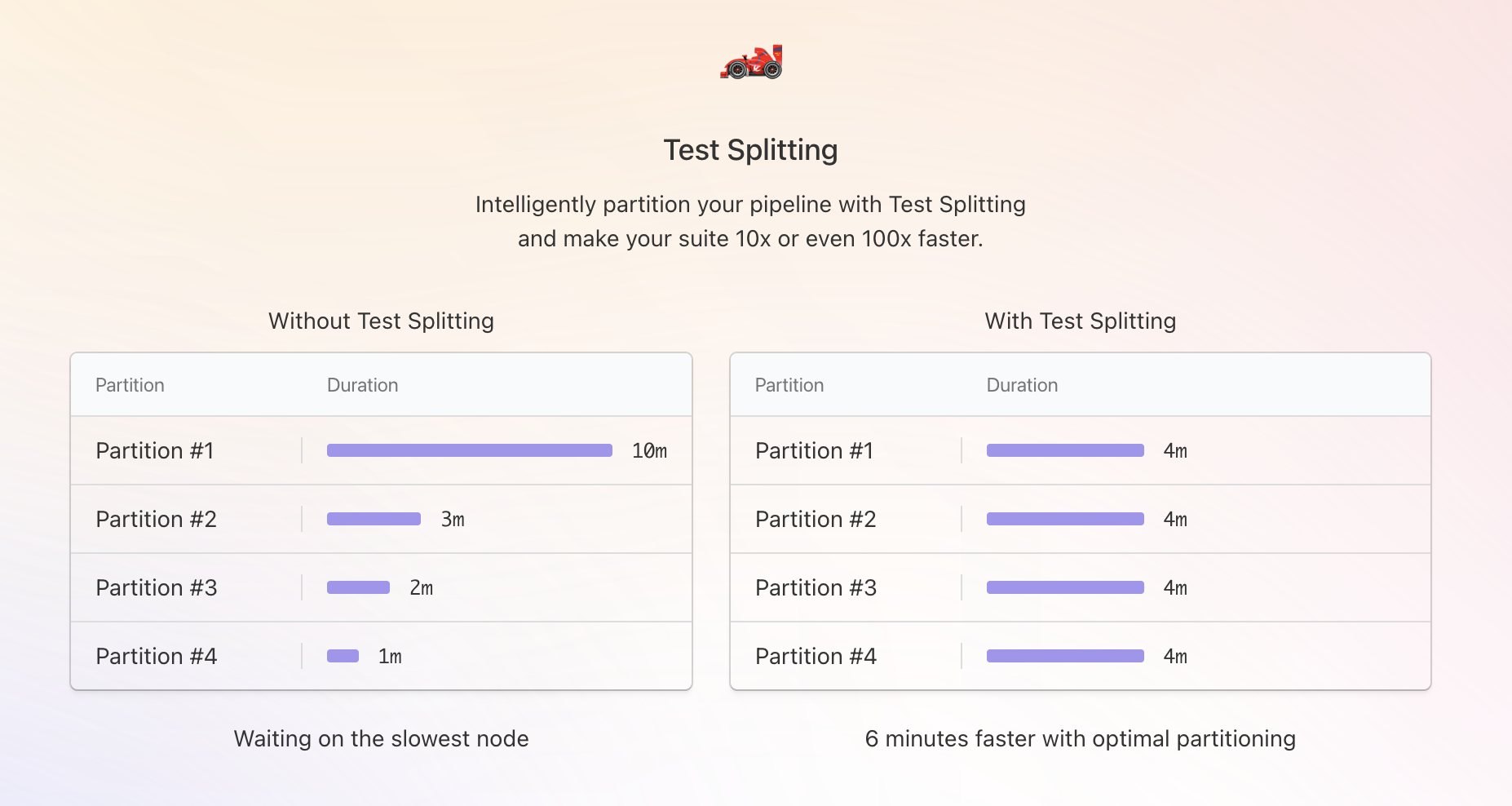
To get started, install the Test Engine Client to:
- Automatically split tests evenly across parallel jobs.
- Quarantine unstable tests based on customizable heuristics.
For full setup instructions, see the Test Engine docs.
Ming
Al
Label your tests with Test Engine
You can now label your tests with Buildkite Test Engine!
Labels allow you to:
- Organize tests to be more meaningful to your team and organization.
- Categorize tests, and therefore, can be used to filter tests within Test Engine.
Labels may be applied to or removed from tests:
- Manually through the Buildkite interface.
- Automatically through the automatic quarantine or test execution tags features.
- Using the REST API.
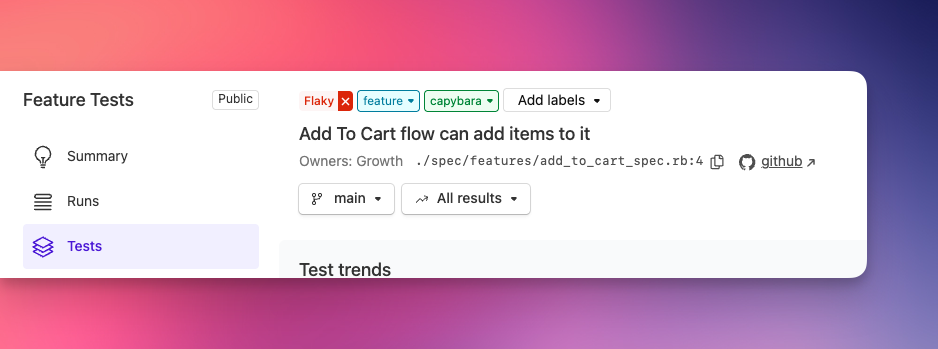
Start labelling your tests with Test Engine today.
James
Extended preview phase for the new build page
We're extending the preview period for our new build page beyond the originally announced April 24th date. This extension gives us time to incorporate your valuable feedback and implement several significant enhancements before making it the default experience.
Why we're extending
Your feedback has been instrumental in shaping the new build page. We're working on performance optimizations and feature additions based directly on your input, with some substantial improvements in the pipeline.
Rather than rushing these changes, we want to:
- Complete the implementation of key performance improvements
- Incorporate requested features that enhance your workflow
- Ensure a seamless transition when the new experience becomes the default
What's next
We remain fully committed to the new build page with its enhanced navigation, powerful table views, improved build management, and better annotation support. If you haven't tried it yet, we encourage you to opt in through the button on any build page.
When our next wave of improvements is ready, we'll announce a new deprecation timeline for the classic build page, giving everyone ample time to adjust to the changes before they become standard.
Please continue sharing your feedback at support@buildkite.com - it directly influences our development priorities.
Chris
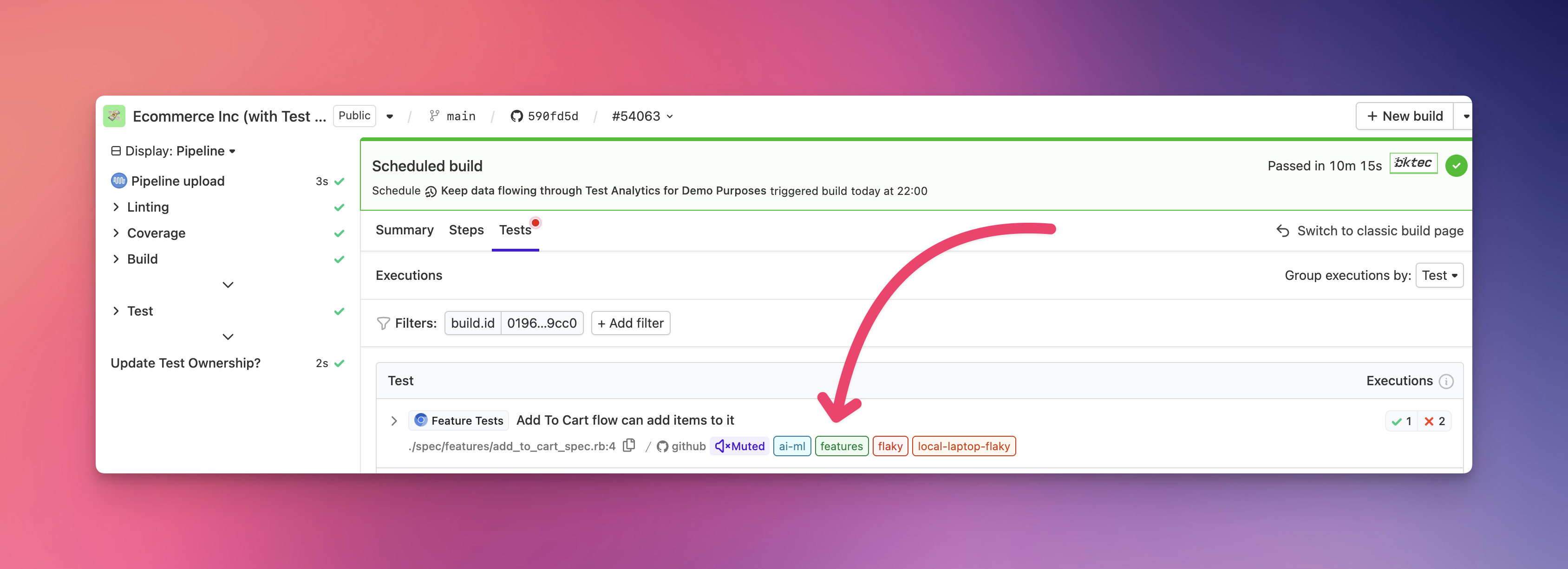
Custom tagging for tests
You can now add custom tags to your tests — unlocking a whole new dimension (literally) of insight and control.
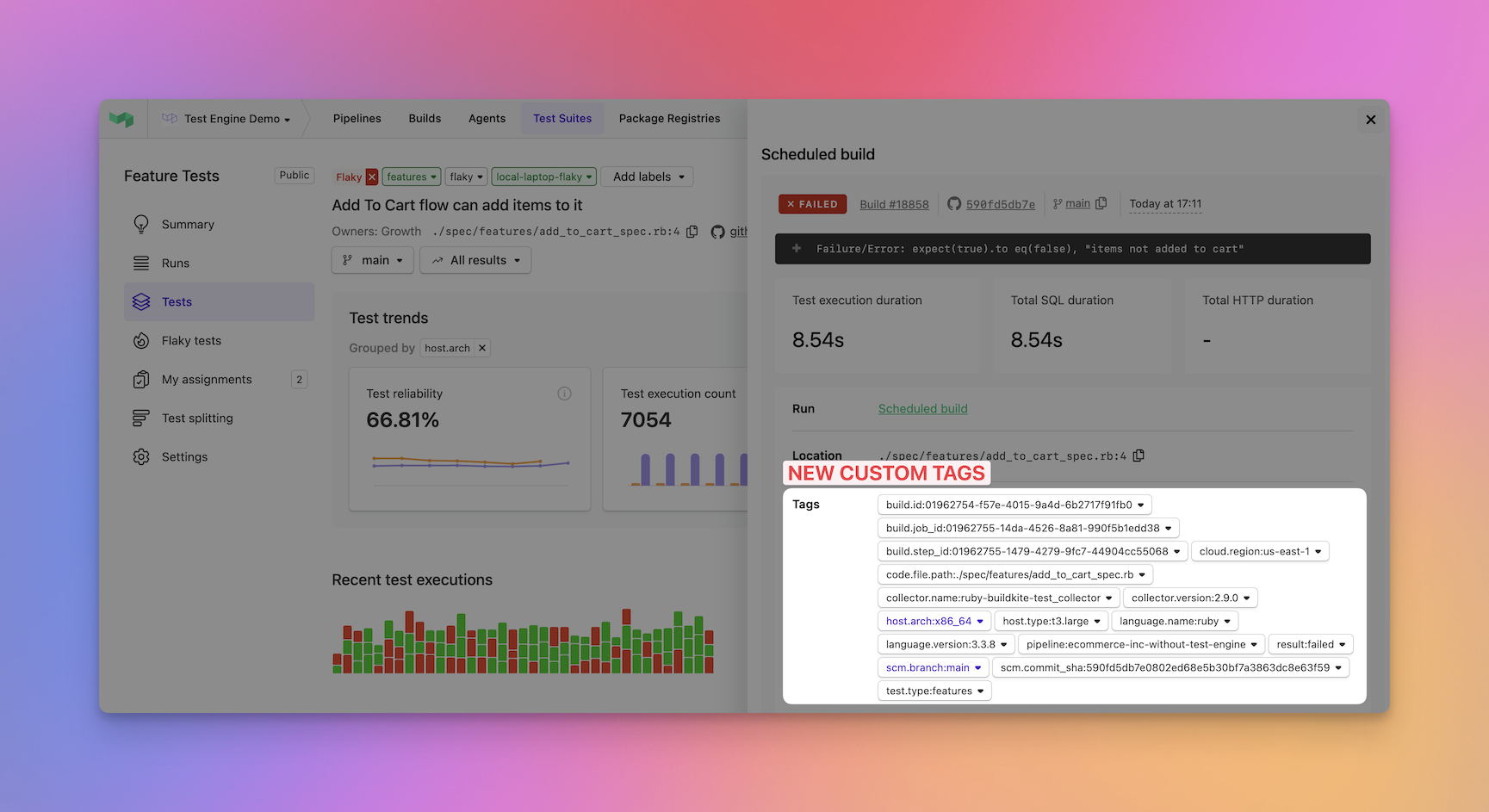
Whether you want to tag tests by the infrastructure they run on, the services they touch, or framework versions they depend on, custom tags let you define what matters — and then slice your test data by those attributes.
🔍 Find root causes faster
Spot patterns in failures and slowdowns by breaking down your suite along your real-world dimensions — like container image, compute pool, or dependency version.
📊 Insights tailored to your stack
Move beyond generic test metrics. Aggregations by custom tags give you visibility into the things that actually cause pain in your CI.
💸 Drive cost and performance optimizations
Use tags to identify high-cost, slow, or flaky tests by environment — and target improvements where they’ll have the biggest impact.
Start tagging your tests with Test Engine today.
James
Removed changelog from GraphQL API
The Changelog, ChangelogAuthor, ChangelogConnection, and ChangelogEdge types have been removed from the GraphQL API.
Please use the changelog Atom feed (https://buildkite.com/changelog.atom) instead.
Juanito
Start turning complexity into an advantage
Create an account to get started for free.

